Audit Trail Overview
Overview
The TruthVouch Audit Trail is an immutable, hash-chained log of every AI request, governance decision, and policy violation — automatically captured and verified. It provides complete accountability for auditors, regulators, and your security team.
What Gets Logged
Per Request
- Timestamp: UTC, millisecond precision
- User/Agent: Who made the request
- Model: Which AI model (gpt-4, claude-3, etc.)
- Request Text: Full user input (encrypted in storage)
- Response Text: Full AI output (encrypted in storage)
- Latency: Time taken to process
- Token Count: Tokens used
Policy Decisions
- Policies Evaluated: Which policies ran
- Policy Results: Pass, fail, or warning
- Actions Taken: Block, warn, log, or allow
- Reason: Human-readable explanation
- Approver: Who approved if manual approval
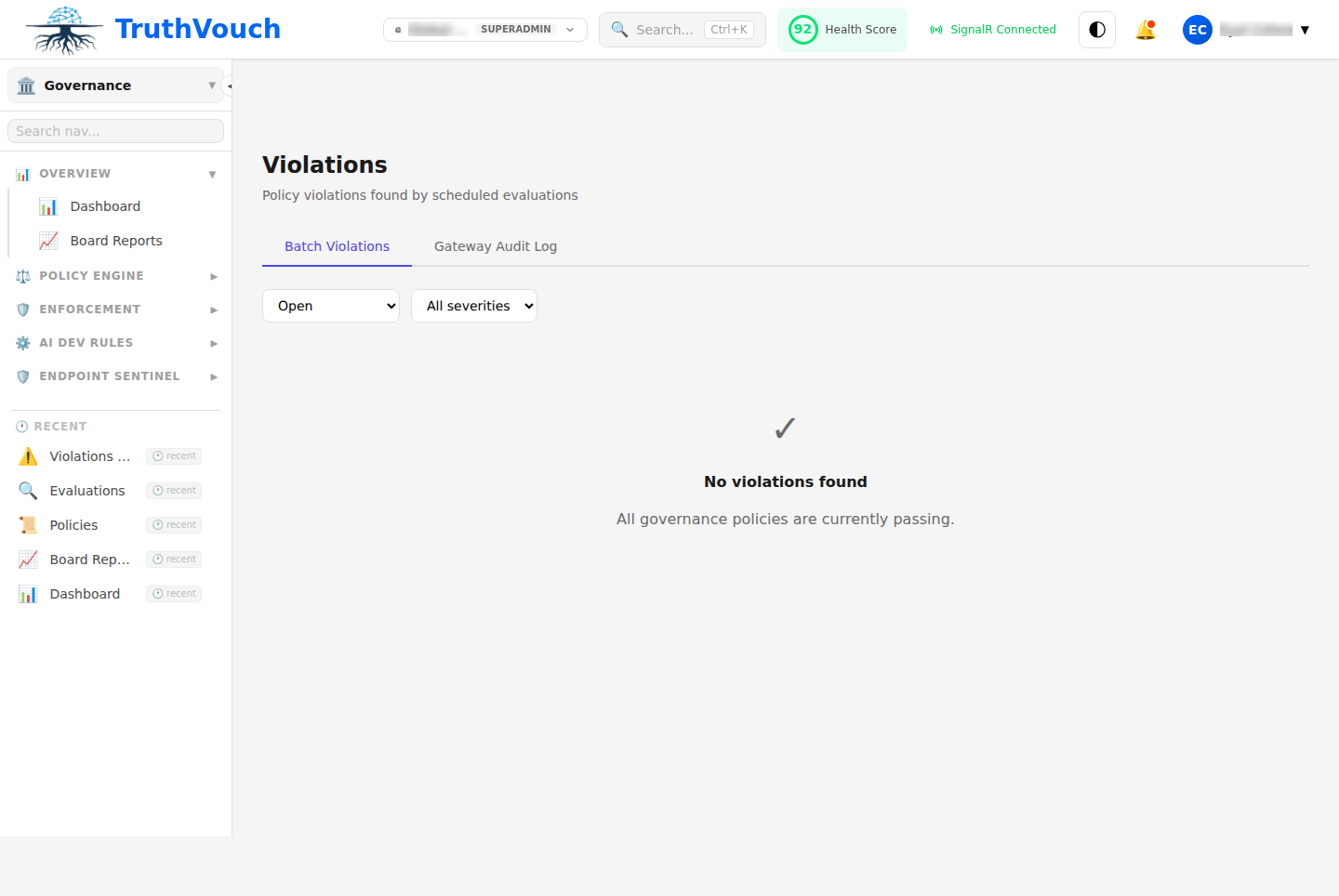
Violations
- Violation Type: PII, injection, content safety, etc.
- Stage: Which firewall stage detected it
- Confidence: How sure the detection was
- Details: Specific pattern matched, entity type, etc.
- Action: Block, redact, mask, or warn
Changes
- Configuration Changes: When settings change
- Policy Deployment: When policies go live
- Rule Updates: When custom rules change
- Access Changes: Who got/lost access
Immutability & Integrity
The Audit Trail uses cryptographic hashing to prevent tampering:
Entry 1: [Request Data] → SHA-256 Hash AEntry 2: [Policy Decision] → SHA-256(Hash A + Entry 2 Data) = Hash BEntry 3: [Violation] → SHA-256(Hash B + Entry 3 Data) = Hash C...Verification:
- Download audit export
- Run verification command:
truthvouch audit verify --file audit.json - If any entry was modified, verification fails
- Auditors can independently verify integrity
Data Retention
| Data Type | Retention | Searchable | Compliance |
|---|---|---|---|
| Audit Entries | 90 days (default, configurable to 2 years) | Yes | SOC 2 |
| Encrypted Request/Response | 30 days (configurable) | Via filters, not full-text | GDPR |
| Metadata | Indefinite | Always | All |
| Deleted Entries | After retention + 30 days soft delete | No | GDPR Right-to-Delete |
To extend retention:
- Go to Settings → Audit → Retention Policy
- Increase days (1-730)
- Note: Longer retention = more storage cost
Access Control
Only authorized users can access audit logs:
Roles
| Role | Can View | Can Export | Can Delete |
|---|---|---|---|
| Admin | All | All | Yes (with reason) |
| Security Lead | All | All | No |
| Auditor | All | All formats | No |
| Compliance Officer | All | PDF/JSON | No |
| Regular User | Own requests only | Own only | No |
Field-Level Filtering
Some fields are masked unless you have explicit access:
- Response Text: Redacted unless you have “view-responses” permission
- Request Details: Partially visible unless “view-requests” permission
- User Identity: Name redacted for privacy unless specific access
Example (Regular User view):
{ "timestamp": "2025-03-15T10:23:45Z", "user_id": "user_***", "model": "gpt-4", "request_text": "[REDACTED - Request text visible only to admins]", "response_text": "[REDACTED - Response text visible only to admins]", "latency_ms": 145, "decision": "allowed"}Log Entry Structure
Standard Request Log
{ "id": "log_abc123def456", "timestamp": "2025-03-15T10:23:45.123Z", "sequence_number": 1547932, "hash": "sha256:abc123...", "previous_hash": "sha256:xyz789...",
"user": { "id": "user_12345", "email": "john@company.com", "department": "engineering" },
"request": { "model": "gpt-4", "prompt": "[ENCRYPTED]", "tokens": 245, "parameters": { "temperature": 0.7, "max_tokens": 2000 } },
"response": { "text": "[ENCRYPTED]", "tokens": 412, "latency_ms": 2145 },
"governance": { "policies_evaluated": ["pii-check", "safety-check", "model-approval"], "policies_passed": 3, "policies_failed": 0, "violations": [], "decision": "allowed", "scan_latency_ms": 85 },
"firewall": { "stages_run": [ {"name": "rate-limiter", "status": "pass", "time_ms": 1}, {"name": "pii-scanner", "status": "pass", "time_ms": 8}, {"name": "content-safety", "status": "pass", "time_ms": 20}, {"name": "truth-scanner", "status": "pass", "time_ms": 42} ] }}Violation Log
{ "id": "log_xyz789abc", "timestamp": "2025-03-15T10:25:12.456Z", "sequence_number": 1547933, "hash": "sha256:def456...", "previous_hash": "sha256:abc123...",
"user": { "id": "user_12345", "email": "jane@company.com" },
"request": { "model": "gpt-4", "prompt_summary": "Contains PII: email, phone" },
"violation": { "type": "pii_detected", "stage": "input-pii-scanner", "entities": [ { "type": "email", "value_redacted": "j***@company.com", "confidence": 0.98, "position": "45-62" } ], "decision": "blocked", "message": "Request contains PII; please remove before submitting" }}Viewing the Audit Trail
Dashboard
Navigate to Governance → Audit Trail:
- Browse latest entries (newest first)
- Click any entry to expand full details
- See all firewall stages and policy results
- View encrypted request/response (if authorized)
Filtering
Quick Filters:
- Time range (Last hour, day, week, month, custom)
- User (specific user or all)
- Model (gpt-4, claude-3, etc. or all)
- Status (allowed, blocked, warned)
- Violation type (PII, injection, toxicity, etc.)
Advanced Search:
user:john@company.commodel:gpt-4violation:pii_detectedtimestamp:[2025-03-01 TO 2025-03-15]decision:blockedExport
Download audit logs in multiple formats:
- JSON: Full entries with all data
- CSV: Structured data for spreadsheets
- PDF: Formatted report for printing
- SIEM: Forward to security systems
See Audit Export & Compliance for details.
Compliance Framework Mapping
SOC 2 Type II
CC7.2 System Monitoring:
- Audit trail logs all access and changes
- Hash verification ensures integrity
- Retention meets audit requirements
CC6.1 Access Control:
- User identity recorded
- Role-based access to audit logs
- Change approval documented
ISO 42001
4.4 Governance Monitoring:
- AI system usage logged
- Policy compliance recorded
- Violations tracked and reported
EU AI Act
Article 9 Transparency:
- Complete log of AI use
- Decisions and reasoning documented
- Available for regulatory inspection
GDPR
Article 32 Security:
- Encryption of sensitive data
- Access logs prove no unauthorized viewing
- Data retention matches GDPR requirements
Article 17 Right to Delete:
- Soft delete: entry marked deleted but hash chain preserved
- Hard delete: after retention period
Real-World Example
Incident Response Scenario:
2025-03-15 10:23:45 - User john@company.com requests summary of customer data → Policy evaluation: PII check = PASSED → Firewall: PII scanner = PII DETECTED (email address) → Decision: BLOCKED - "Contains customer email" → Audit logged
2025-03-15 10:24:12 - john@company.com retries with PII redacted → Policy evaluation: All PASSED → Decision: ALLOWED → Response processed → Audit logged
Security Team Reviews Later: 1. Go to Audit Trail 2. Filter: user:john@company.com timestamp:[2025-03-15] 3. See both attempts 4. First one shows john attempted to send unmasked PII 5. Second one shows he complied with filtering 6. Audit demonstrates governance working as designed 7. Export audit entries for SOC 2 auditorPerformance Considerations
The audit trail is designed for minimal latency impact:
- Async Logging: Entries logged to database asynchronously (doesn’t block request)
- Encryption: PII data encrypted, minimal CPU impact
- Indexing: Optimized for fast queries and filtering
- Archival: Old entries moved to cold storage automatically
Typical overhead: <5ms added latency per request.
Best Practices
- Review Weekly: Spend 15 minutes reviewing high-level stats
- Set Alerts: Configure alerts for suspicious patterns
- Preserve Evidence: Keep exports for compliance proofs
- Verify Integrity: Periodically verify audit hash chain
- Retention Planning: Plan for storage growth over time